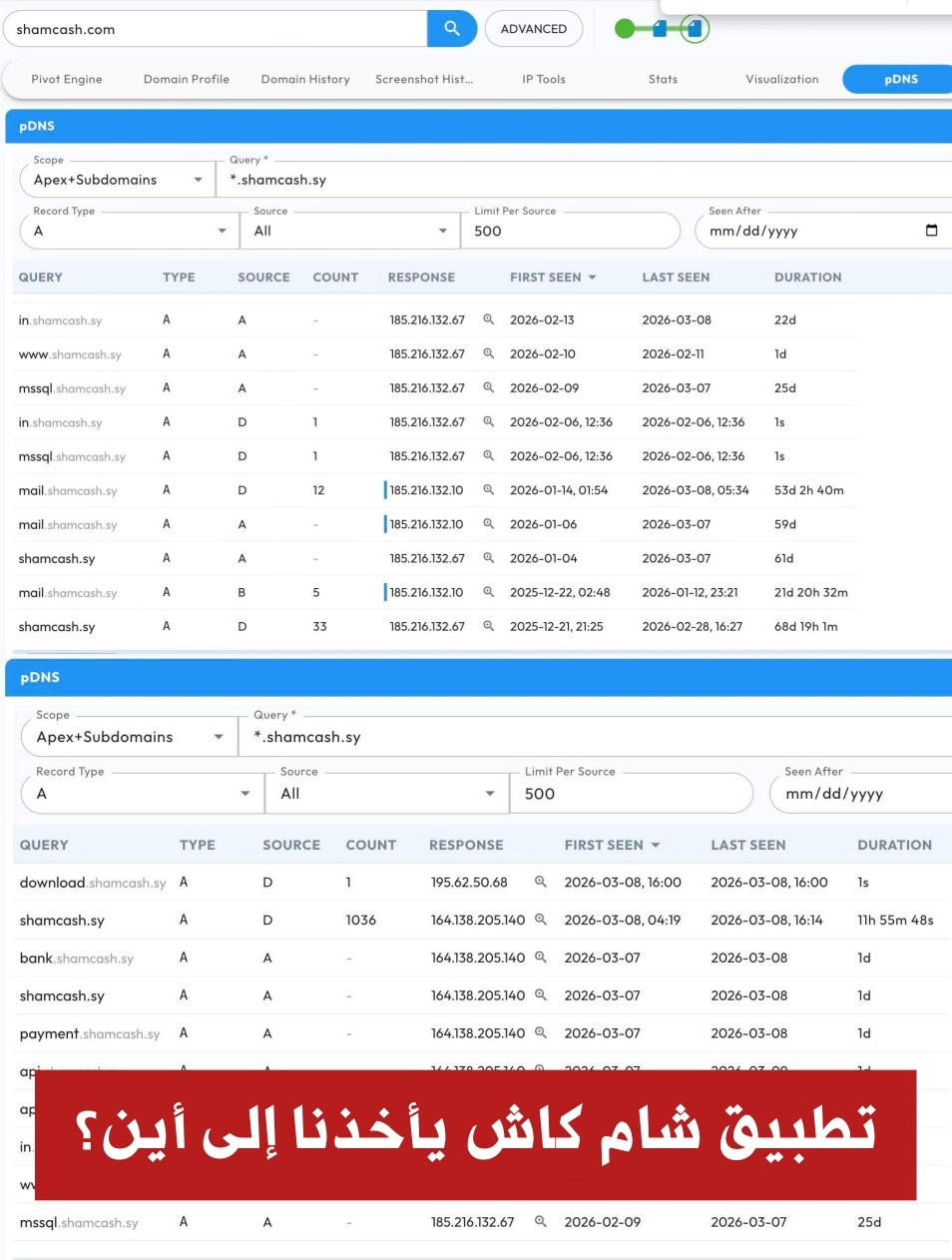
In a highly sensitive technical analysis, expert Dilshad Othman revealed that the "Sham Cash" application has moved to a new domain, shamcash[.]sy. Following its recent shutdown, this move was more than just a technical change; it exposed security vulnerabilities related to the management of official servers in Syria and the application's connections to opaque development companies.
Government Servers "Unlicensed"
According to the analysis, the application's subdomains point to a Syrian IP address (185.216.132[.]67) belonging to the "National Network Services Authority." The shocking aspect is that this server not only hosts the application but also houses several important and sensitive government websites under the control of the "Plesk" control panel.
Why is this dangerous?
A vulnerability in a single location on this server allows attackers to perform what is known as "lateral movement," meaning they can easily compromise other government websites and applications hosted on the same server. The expert has already identified three security vulnerabilities, one of which is "very serious":
- CVE-2020-35886
- CVE-2020-35888
- CVE-2024-56
"Shameful" Technical Negligence
The problem wasn't limited to software vulnerabilities; it extended to "primitive" security management. Highly sensitive public internet ports were opened, such as:
- FTP & MSSQL: direct gateways to databases and file transfers.
- Email ports: making the server vulnerable to spam attacks and direct hacking.
Osman described this level of work as "very unfortunate and shameful," indicating that the country appears to be "compromised from its core" due to this negligence.
Shamlogix Threads and Turkish Connections
The analysis traces a company called shamlogix[.]com, registered in May 2025, which is believed to be the application's API developer. What's suspicious is that the company lists the names of developers and designers on its website, but completely hides the names of the owners.
Furthermore, tracking revealed that the company uses Turkish IP addresses (164.138.205[.]134) located in Idlib, and employs an open-port Mikrotik router with publicly controlled access and no VPN or firewall protection, reflecting a complete disregard for security.
Conclusion: A Data Blast Is Coming
The data confirms that what happened to ShamCash recently wasn't just a traditional technical breach, but rather the exploitation of structural vulnerabilities in an inherently illegal application.
With this deplorable level of security, the tech expert predicted that the application was indeed compromised, suggesting a massive data dump for users is imminent.
Zaman Al Wasl
















Comments About This Article
Please fill the fields below.